A few months ago a steel mill in Germany suffered serious damage when their blast furnace couldn’t be shut down. On investigation, it was determined that someone had opened a phishing message and allowed hackers access to the controls.
Phishing is the sending of deceitful email messages designed to get you to open an attachment that can infiltrate your computer system, or to get you to share your password with a hacker. You might get emails telling you that your bank account has been compromised and you need to give your password to get back into your online account. That’s a common type of phishing method.
Cybersecurity in factories is often pretty dismal, and it probably should be updated in your plant. Some of the best things you can do:
- Make sure that business systems are separate from production systems: a firewall is the least you should have.
- Watch out for shadow IT systems which could compromise your security.
- Train operators in security practices.
But it doesn’t make sense to get too carried away. An Automation World columnist recently wrote, “Cybersecurity requires a shifting of priorities for plant managers who are more worried about cost pressure, an aging infrastructure, productivity improvement, workforce attrition, and operational excellence. Let’s face it, none of that matters if a massive security breach causes irreparable damage.”
Well, yes, it does matter. First, the German steel mill was only the second case ever in which physical damage was caused by a cybersecurity breach. How much damage has been caused by cost pressures, an aging infrastructure, workers trying to meet increased productivity demands, new workers with inadequate skills, and a lack of operational excellence?
Second, doing things right lessens the chances of damage, and it’s essential up to the point of damage and after the damage has been dealt with.
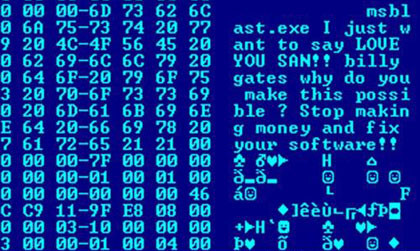
Third, we’re not talking here about criminal masterminds using futuristic tools to creep into a system. The hackers were knowledgeable about industrial systems and were able to move fast once they breached the system,but they didn’t do that in a particularly clever way. Someone let them in. This is the most common point of failure in cybersecurity systems. We walk away from a logged-in computer. We use the same password — our birthday or our dog’s name — for a decade. We post log in information on the wall with a sticky note. We pay attention to the blandishments of Nigerian princesses.
Cybersecurity shouldn’t be ignored. It should be part of operational excellence.
